IT Governance & Security
IT Risk Management Solutions to Protect Your Reputation
In today’s digitized world, IT governance and security are top priorities. System downtime, fraudulent activity, and data breaches are among the many cybersecurity mishaps that threaten a company’s success.
Protect your company’s data, customers, and reputation with LogicManager’s IT Risk Assessment & Security Software.
- Ensure your sensitive information is stored in compliance with evolving privacy requirements through readiness guidance and risk assessments, along with data mapping and incident response management.
- Align policies and procedures to best-practice frameworks and regulations like ISO, NIST, COBIT, GDPR, CCPA, and more.
You might also like:
Why Logicmanager? – Users of LogicManager’s ERM software explain how their ITRM programs have benefited from our platform and expert advisory service.
Customer Success StoriesExplore How Companies Overcame Challenges With Our IT Risk Management Solutions
ERM Can Save Millions: Cybersecurity Case Study
A Santa Barbara based non-profit organization suffered a breach of over 30,000 medical records caused by a third-party vendor that housed personal health information (PHI) without adequate security measures to safeguard the data, a disaster that could have been prevented with proper cybersecurity risk management.
The Advantages of SaaS in Large GRC and ERM Deployments
Take a close look at a large, multinational manufacturer aiming to identify and assess risks across all departments in this case study and learn why LogicManager’s Software-as-a-Service delivery model offers an ideal implementation process for large companies looking for an ERM solution.
What Our Customers Are Saying...
The LogicManager DifferenceA Holistic Approach to IT Risk Management (ITRM)
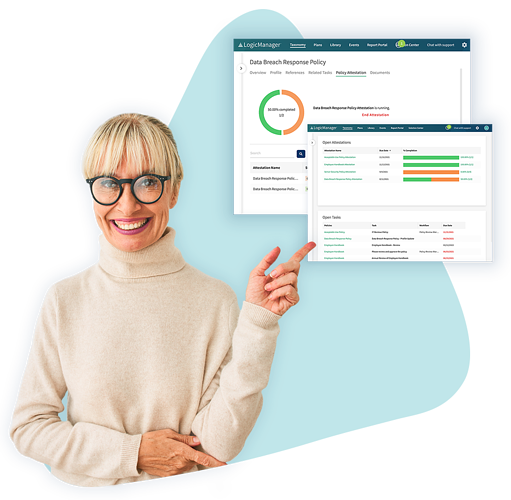
Business Decision InsightsFocus on What’s Important
Through our ERM software, we allow our customers to spend more time strategically managing risks– and less time on tedious administrative activities, like data cleansing and manipulation. Our solution enhances efficiency while bringing “unknown knowns” that risk managers might miss to the surface. Stay on top of ever-changing standards, regulations, and emerging threats while keeping your company’s customer and employee data safe.
Customer ExperienceStreamline Your Risk Management Program
Unlike other software that requires IT professional customization, our solution allows customers to control engagement through an end-user configuration. This approach enables faster time-to-value and allows organizations to evolve their programs over time, not to mention a quicker return on investment.


Risk-Based ApproachPrepare for Tomorrow’s Surprises Today
A risk-based approach is the key to effective governance, risk, and compliance. This process enables sound prioritization across organizational silos, identifies challenges and critical dependencies, and proper resource allocation. With a risk-based mindset, organizations can better deploy resources to valuable areas, and high-level risk concerns can more easily surface– and be appropriately mitigated.
CapabilitiesAn All-In-One IT Risk Management Platform
Frequently Asked QuestionsFoundations of IT Risk Management
According to Gartner, IT risk management (ITRM) products are “software and services that operationalize the risk management life cycle of cyber and IT risks in the context of an organization’s mission. ITRM products are deployed to establish a central hub that facilitates business-related risk management.”
System downtime, fraudulent activity, and data breaches can threaten a company’s success.
In today’s business environment, technological advancements routinely outpace regulatory requirements and standards. Such advancements prove to be a double-edged sword; although this streamlines operational capacity, reduces costs, and increases efficiency, it also opens up new vulnerabilities. New technologies mean new tools for both businesses and attackers alike, but the more you rely on technology, the more exposed you are to related weaknesses. Some common cybersecurity threats today include:
- Hacking, resulting in data loss or theft
- Impersonation of executives to retrieve confidential information
- Knowledge, privilege, or data abuse
- Unapproved hardware or software installation
- Polymorphic malware
Related SolutionsYou May Also Like…
Request a DemoLearn How LogicManager’s IT Governance & Security Software Can Transform Your ITRM Program
Speak with one of our risk specialists today and discover how you can empower your organization to uphold their reputation, anticipate what’s ahead, and improve business performance through strong governance.