How to Tackle The Top Three Risks in the Energy Industry
Steven Minsky | March 6, 2019

For the first time, reputation risk, organizational culture, and cybersecurity have all landed among the top five risks in the energy industry. How can energy companies tackle all of these risks without wasting time and money on additional resources?
This year at my IRMI Energy Risk and Insurance Conference session, I showed attendees how they could tackle all three of these top-priority risks with enterprise risk management.
The key is adopting a truly integrated approach to risk management. The truth is, energy companies already collect much of the information they need to build a mature risk management program. More often than not, however, organizations fail to engage all departments and levels of the organization to share this information cross-functionally and to the right levels to make decisions.
During my session at 2019 IRMI ERIC, I walked attendees through, step-by-step, how their organizations can implement a risk-based approach to build a risk culture and cybersecurity program that mitigates reputational risks before they occur.
Whether you made it to this year’s conference or not, I wanted to share some of my takeaways from the session, as well as some tools I presented to facilitated a risk-based approach.
Emerging Risks in the Energy Industry
According to the report “Executive Perspectives on Top Risks 2019”, energy and utility companies rated organizational risk to have a ‘significant impact’ on operations in response to the following statement: “Our organization’s culture may not sufficiently encourage the timely identification and escalation of risk issues that have the potential to significantly affect our core operations and achievement of strategic objectives.”
Interestingly enough, when asked about reputational risk such as social media, energy and utility companies responded with a ‘potential impact’ rating.
What every company must realize is that in a See-Through Economy, social media is directly tied to reputational risk, which is in turn tied to the achievement of strategic objectives, and often related to cyber risk.

Deepwater Horizon Drilling Unit on Fire, Wikipedia
To drive home the importance of these emerging risks, I revisited some of the biggest scandals in the energy industry, such as the Merrimack Valley Gas Explosion, the PG&E electric fires, and of course, the Plains All American Pipeline Spill. Each of these mishaps carried immense reputational risk, and more importantly, were 100% preventable because they stemmed from severe negligence.
Mitigate Energy Risks with the Right Tools
So how can you prevent negligence and corporate mishaps in the energy industry?
It all starts with having the right tools. At IRMI ERIC, I presented two physical tools attendees could use every day to facilitate a risk-based approach.
First, I showed them LogicManager’s Risk-Based Approach Wheel, which gives great visual insight into the activities performed during an end-to-end, iterative ERM process. You can download the Wheel here.
I also introduced them to another one of my favorite tools – the Risk-Based Translator. Often times, organizations have a lot of trouble communicating about risk because each department has their own secret lingo of sorts. Download the Translator here to see how you can create a common language across departments.
Get Risk-Based
Download our Risk-Based Approach Wheel to visualize how different governance activities fit together in one iterative process.
One question I got from an attendee was how to actually engage people. I answered with one of my favorite approaches: get someone in the C-suite in your corner. Try giving a heads up to a risk-minded C-suite executive that you’ll be sending out a risk assessment to key departments. Ask him or her to send out an email to everyone involved, directly thanking those who completed the assessment and expressing how important it is for the company. Then, more people will follow suit and complete the assessment!
Tackling Cyber Risk in the Energy Industry
The best way to get a risk-based approach up and running is to take it one initiative at a time. In my presentation, I focused on one of the top risks in the energy industry: cybersecurity. This was a great example to use, not only because of its prevalence in the industry, but because it is deeply connected to reputational and organizational risk, as you can imagine.
Just recently, in fact, the North American Electric Reliability Corporation (NERC) fined an energy company $10 million for over 100 physical and cyber security violations to the regulatory authority’s Critical Infrastructure Protection (CIP) standards. It’s the biggest fine NERC has ever levied for CIP violations.
Complying with a standard such as CIP is a huge, cross-functional effort in and of itself. When you come to terms with the fact that compliance is the minimum operating standard, protecting your organization from cyber risk becomes an even larger task.
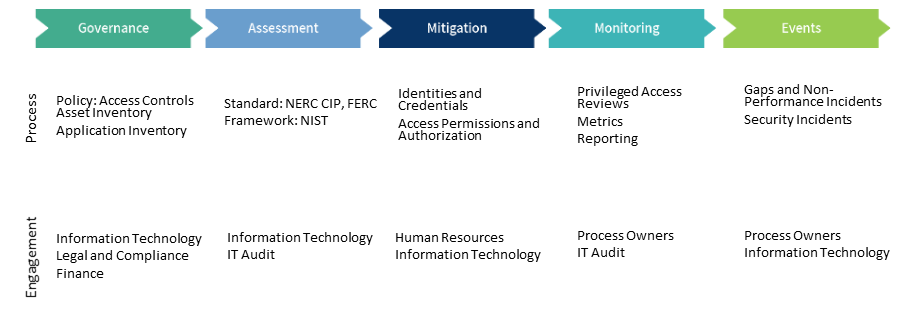
At IRMI ERIC 2019, I advised my audience to take the following steps:
- Break down a standard like NERC CIP into actionable, bite-sized line items and determine which departments they impact
- Pick one of these line items, such as required access controls and identify where your organization is excelling and where there are gaps by administering standardized risk assessments to impacted departments
- Once this information is collected, start filling in the gaps with new mitigation activities like dual authentication procedures, password vaults, entitlement policies, etc.
- Implement ongoing monitoring activities like privileged user access reviews; consider automating these processes with regularly recurring reminders and notifications
- Make sure there is a standardized method for reporting incidents like security and non-performance events
Learn More About Cybersecurity
Download our eBook on taking a risk-based approach to cybersecurtiy to learn more about these steps in-depth.
As always, I would also recommend doing a health check of your ERM program and processes. The best way to do this is by taking the Risk Maturity Model, which has been recommended by the American Petroleum Institute. You can take the free Risk Maturity Model assessment here to see how your program stacks up against industry standards.
The energy industry, like many others such as the insurance industry, is coming to terms with the fact that risks are interdependent. If risks are intertwined, then it can only follow that departments must also be intertwined, and must work together to protect their organization and prevent risks from blooming into disaster through an integrated approach.