3 Steps to Better User Access Reviews
A user access review involves examining your organization’s IT applications and reviewing which ones are available to which employees, third parties or other stakeholders. But like most business processes, user access reviews are not a once-and-done activity that can be completed by one person; there is an ongoing monitoring piece that involves ensuring your user access reviews have been completed.
It’s important to take a risk-based approach to user access reviews to ensure they’re providing the intended business value of ensuring a separation of duties and mitigating threats like privilege creep, excessive privileges, access misuse and employee mistakes. This ultimately ladders up to the end goal of preventing disastrous IT risk events like ransomware attacks (which are more prevalent than ever before) or fraud. Performing user access reviews is also a requirement of many IT regulations, such as NIST, HIPAA and PCI DSS. These risk events can quickly cause a negative impact financially and damage your reputation.
Simply putting controls in place to mitigate privileged access abuse threats can only do so much to prevent them from materializing. This guide will walk through 3 key risk-based practices that will not only increase the effectiveness and efficiency of your user access review process, but also ensure that a risk event never snowballs into a scandal or long-term business disruption.
COMPLIMENTARY DOWNLOAD:
Risk Assessment Template for Excel
COMPLIMENTARY DOWNLOAD:
Risk Assessment Template for Excel
Our free, easy-to-use risk assessment template allows to complete risk assessments in Excel to better mitigate risk, direct your business strategy and much more.
STEP 1: Standardize and formalize your processes
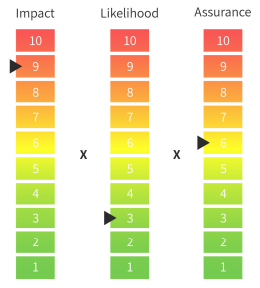
LogicManager has long believed that an Enterprise Risk Management (ERM) methodology, also known as a risk-based approach, is the best way of accomplishing any type of organizational governance. With risk as the common factor, governance activities like user access reviews inherently become standardized and comparable, enabling better decision-making and ensuring consistency across all departments and timeframes. One of the best ways to standardize your approach is by performing comprehensive and objective risk assessments.
Once you’ve standardized the way you identify and assess risks to your organization’s applications, it’s important to formalize your processes. Formalization is especially critical when it comes to user access reviews because by nature, it’s a process that must be performed frequently and consistently. Implementing policies that users and managers must understand and agree to adhere to is an excellent way of ensuring that everyone is working towards the same goal. At the very least, it prevents 100% of negligence penalties.
STEP 2: Work smarter, not harder
Depending on the size of your organization, user access reviews can be an incredibly tedious and time-consuming process. Despite needing to sift through hundreds or thousands of users, many people still rely on memory and manual labor to true up their user lists. Instead, this process could be streamlined from start to finish using the power of software automation.
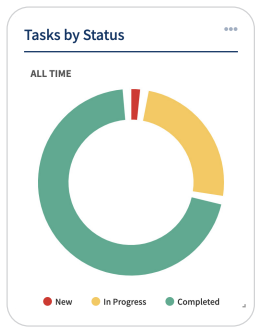
Through a risk-based approach, you’ll proactively assess which of your applications are highest risk and most critical to your organization. This allows you to better prioritize your time and resources and perform more frequent or in-depth access reviews only where it’s necessary. From there, ERM software like LogicManager provides a library of automated tasks and workflows that can be implemented in your environment for streamlining the entire review process. There are automations to help you manage the process and stay ahead of responsibility shifts, like scheduling tools, Suggested Mitigations AI and “set it and forget it” tasks, as well as no-code integrations with applications like Jira so you can complete the user access reviews and seamlessly upload data directly to your risk environment. The ROI of these automations pays dividends in both hard and soft dollar savings.
STEP 3: Gain a holistic view
Businesses are constantly evolving, so user access reviews must account for changes in every corner of the enterprise. But finding out who has access to what applications, physical resources or privileged information at your organization can be tedious without having a bird’s eye view.

Through ERM software, you’ll be able to connect the dots and maintain a holistic view of your organization. LogicManager’s taxonomy framework brings together your employees, the applications they use, the processes they own and even the risks they’re associated with into one centralized repository. This makes it easy to uncover root cause, bridge departmental silos, visualize upstream and downstream dependencies and allocate resources more efficiently and effectively.
Start Taking a Risk-Based Approach Today
As an IT professional in today’s world of rapidly evolving technology, you shouldn’t have to sacrifice security for automation. LogicManager’s ERM software enables you to perform high-quality user access reviews that focus on mitigating security risks, all while providing zero-code integrations and automations to streamline processes across your entire IT department. See how LogicManager’s robust User Access Review solution package helps you mitigate cybersecurity threats, ensure reviews are completed on time and protect your organization:
With sound risk management practices, negligence is 100% preventable. ERM software not only helps you prevent major incidents like ransomware attacks, but it prevents any minor IT incident from escalating into a systemic issue. Tracking your efforts through LogicManager also builds a time-stamped audit trail, which protects you from 100% of negligence claims. This helps provide the assurance you need to succeed in today’s See-Through Economy. Find out how by talking to a risk expert today about your unique business challenges.
