User Access Reviews & Third-Party Spend Management
UAR Software to Protect Your Reputation & Reduce Third-Party Costs
Protect your company’s data and optimize third-party costs with LogicManager’s User Access Review & Third-Party Spend Management solution. Safeguard your organization by conducting thorough User Access Reviews on essential third parties, ensuring the principle of least privileges is upheld to counter security vulnerabilities. Validate proper delegation of license levels and effortlessly identify and curtail redundant license expenses, ultimately resulting in substantial reductions in annual SaaS vendor costs.
- Enhanced Security Oversight: Perform meticulous User Access Reviews on critical third-parties, fortifying your security stance by enforcing the principle of least privileges and minimizing potential security risks.
- License Optimization: Validate the precise allocation of license levels, preventing over-licensing and enabling efficient resource allocation, directly impacting cost savings.
- Strategic Cost Reduction: Unearth unnecessary license expenses, leading to significant reductions in annual SaaS vendor costs, freeing up resources for strategic initiatives and growth.

VETTED BY THE BEST FOR USER ACCESS REVIEWS
Why a Risk-Based Approach to User Access Reviews is important:
LogicManager’s User Access Review Solution
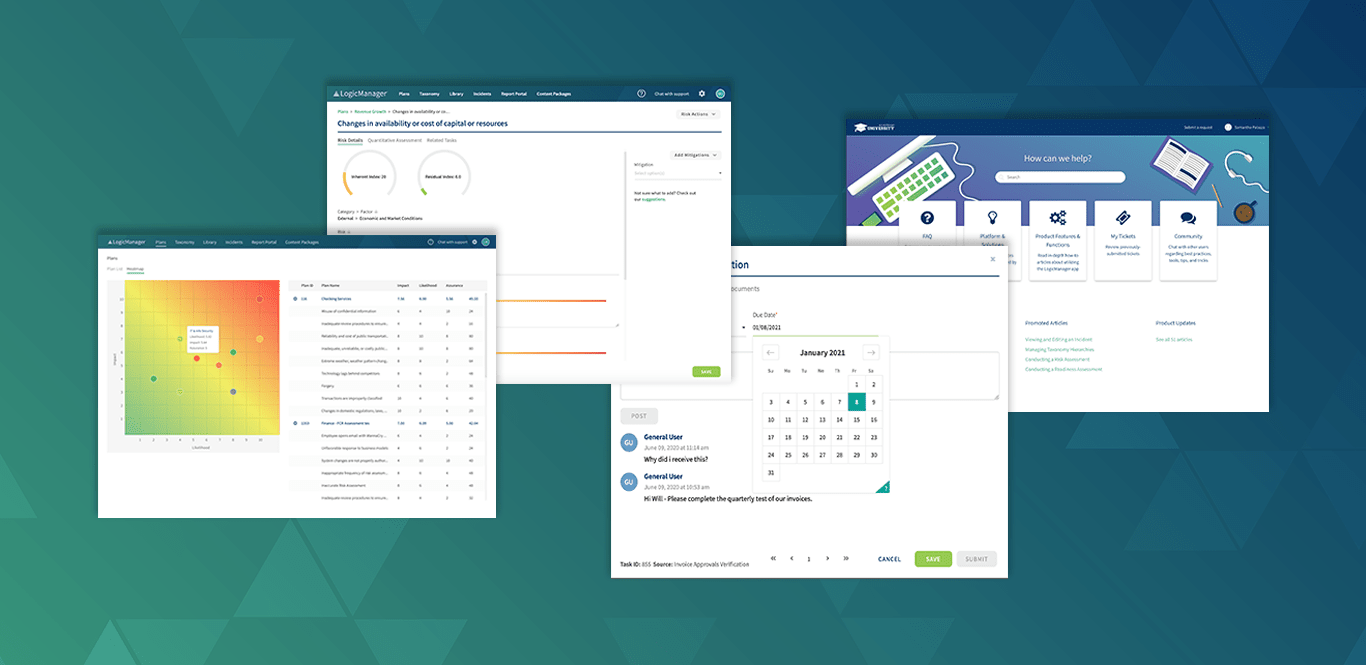
- LogicManager’s Custom Profile & Visibility Rules help you determine the risk level and nature of your applications or physical resources to determine what is the most important information to protect, enforce controls to mitigate your risks and determine the appropriate access review frequency.
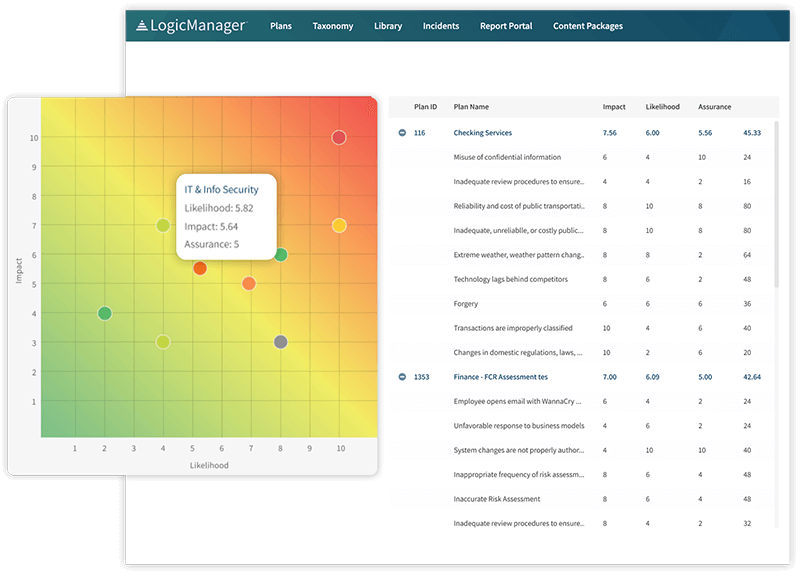
- Personalized home screens bring end users directly to their list of access rights review tasks to ensure access rights reviews are completed on time and Reporting & Dashboard tools generate visualizations that display historical results of user access reviews and a breakdown of user access reviews by status.
- Our Integration Hub allows you to automate and manage your entitlement change tickets including Jira tickets and Active Directory solutions like Azure directly within your LogicManager Workflow system to more easily allocate tasks, facilitate approvals and ensure access rights reviews are completed on time.
- These integrations also power our Event Management system, which allows you to automate the process of engaging managers to review employee entitlements by integrating your recurring file transfer process with LogicManager: simply drop a file into SFTP and sit back as a LogicManager event is created for review and sign-off.
Achieve your User Access Reviews with LogicManager
Protect your information
The most direct benefit of having a formalized user access review process is that you’ll be able to keep access to applications only to those who should have it. This ensures that no unauthorized users or terminated employees are viewing information they could potentially use against you.
Automate your processes
With LogicManager, you don’t need to rely on memory to true up your user lists; set a designated frequency at which you’d like to check your user lists, and have the system pull in the latest user access information and distribute tasks for review.
Satisfy examiners
Building a log of all user access reviews helps demonstrate good governance and shows that you are not negligent. Doing so within a robust system like LogicManager, as opposed to manual spreadsheets and documents, means that you’ll automatically have a full audit trail of exactly when everything was completed.
Cut costs
Through continually performing an enterprise entitlement review where you know who has access to what, you’ll notice more quickly when you’re able to dial back on application agreements that charge per user. Additionally, using a software like LogicManager to perform your user access reviews cuts down the need to assign this task out to people, meaning you’re in a better place to reduce FTE costs if necessary.

What was the real cause of the Colonial Pipeline hack?
One of the most common causes of ransomware attacks is poor user access reviews. Learn how this played a role in the infamous Colonial Pipeline hack, and how ERM software capabilities like automated workflows, task reporting and escalations uncover poor management and prevent disasters before it’s too late.
What is a User Access Review?
Companies everywhere, every day, rely on applications, software and physical assets to power their businesses. These assets house confidential information that only authorized users should be able to access. Therefore, they need to perform a user access review to verify that only the right users have access to that information. It also involves managing entitlements: user or process privileges to perform or have rights to an action on a particular resource).
User access reviews should be performed both periodically (i.e. monthly or quarterly) or on an ad-hoc basis (i.e. an employee has left the company, a third-party contract has terminated, etc.) to eliminate any risks associated with your organization’s private information landing in the wrong hands.
Being responsible for user access reviews also involves providing governance over the policy that dictates access rights and entitlement reviews.
Enterprise Entitlement Review Risks
Should the wrong people have access rights to your company’s sensitive information, a variety of things could go wrong. Making a conscious effort to consistently review who can access what can prevent things like:
- Disgruntled employees using information against you, or leveraging information against your policies for personal gain.
- External fraud and hackers who may access and abuse your employees’ or customers’ personal information.
- Data breaches, which can cause severe reputational damage and impose various financial consequences.
If any of these risks materialize, fines and punishments may be reduced if you are able to prove that you weren’t negligent. If you can demonstrate that you had the proper controls in place (such as user access reviews) you’ll wind up being a lot better off.
Request a DemoLearn How LogicManager’s User Access Reviews & Third-Party Spend Software Can Transform Your IT Risk Management Program
Speak with one of our risk specialists today and discover how you can empower your organization to uphold their reputation, anticipate what’s ahead, and improve business performance through strong governance.