How to Navigate the Cybersecurity Minefield of Remote Work
Last Updated: March 19, 2024
While the debate over the productivity of employees working from home continues to rage, another factor that requires special attention in a hybrid or fully remote company is workplace cybersecurity. According to an INTERPOL report, between January and April 2020, there was a significant increase in malicious cyber activities attributed to the pandemic shift to WFH. These incidents highlight the vulnerabilities introduced by remote work, such as the use of unsecured networks and devices, which can leave gaps for cybercriminals to exploit. In 2024 alone, over 5,360 breaches have compromised more than 30 billion records, signaling a clear and present danger to organizational security.
Companies are expected to establish and maintain a robust cybersecurity posture to protect their customers’ information from cyberattacks and data breaches. This involves implementing security measures, practicing safe online behaviors, ensuring data protection, and responding to security incidents and breaches. A company can be found negligent if they fail to prove they have followed the minimum required cybersecurity measures. Negligence can cost a company millions in the event of a cybersecurity breach, including lawsuits, hefty fines, and irreparable damage to an organization’s reputation. It’s crucial for companies to continuously evaluate and improve their cybersecurity strategies to mitigate risks and comply with legal and regulatory requirements.
What Cybersecurity Risks Do Remote Workers Face?
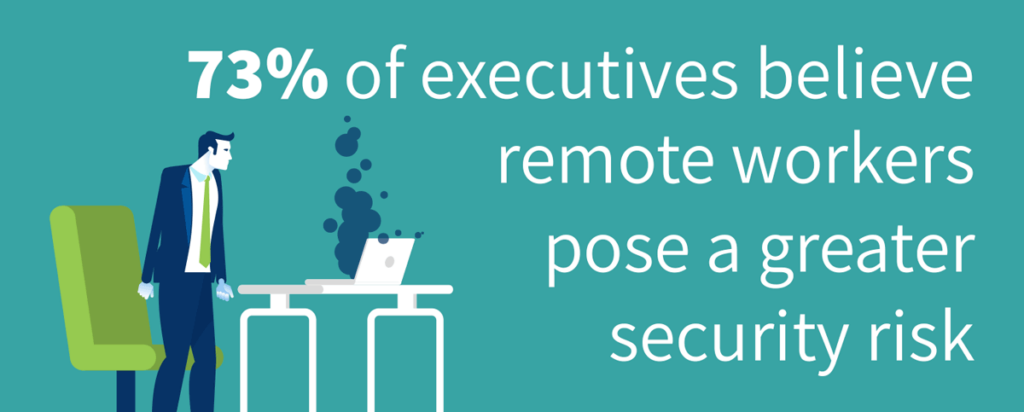
The shift to remote work has introduced a spectrum of cybersecurity risks that organizations must navigate. A growing number of people have started jobs and left them without having once met their colleagues in person. This lack of in-person interaction can increase susceptibility to social engineering and phishing, as remote workers may not have the same level of vigilance outside the traditional office environment. Weak passwords pose a significant threat, undermining even robust cybersecurity defenses like firewalls and VPNs. Cybercriminals exploit these vulnerabilities through various means, including ransomware attacks that hold data hostage and phishing schemes that trick employees into revealing sensitive information.
To combat these risks, continuous training on security best practices is essential. However, the challenges don’t end there. Remote work often involves unsecured networks and personal devices, which lack the stringent protections of corporate IT infrastructure. This can lead to unauthorized access and data breaches, particularly when employees use file-sharing services or connect to corporate resources via unsecured Wi-Fi networks. The use of personal devices, which may not be encrypted or regularly updated, further exacerbates the risk, creating potential entry points for cyberattacks. Organizations must therefore reassess their cybersecurity strategies to effectively protect against the evolving threats posed by remote work.
Cybersecurity Risk Management Best Practices
In the era of remote work, businesses face unique cybersecurity challenges that require tailored risk management strategies. Here are some expert practices to safeguard your remote business:
- Establish a Robust Identity Governance Framework: Integrate a strong identity governance platform within your existing business processes. This alignment ensures that security measures enhance, rather than hinder, productivity. By managing identities effectively, you can maintain a secure yet efficient workflow.
- Maintain a Comprehensive Inventory of Digital Assets: An up-to-date inventory of all infrastructure, applications, services, and devices is crucial. Many organizations lack visibility into these critical assets, which is akin to leaving your digital doors unlocked. Knowing what needs protection is the first step in safeguarding it.
- Understand the Context of Each Connection: Grasp the full context of every connection within your network. Implement stringent identity management, device posture control, and granular application permissions. This approach helps in detecting anomalies and preventing unauthorized access.
- Cybersecurity Education for Remote Teams: Remote team members, often working in isolation, might become complacent about security practices. Regular training on cybersecurity best practices is essential to keep everyone vigilant and informed.
- Manage Risks from Connected Technologies: The integration of generative AI and other advanced technologies into our systems brings new risks. It’s imperative to monitor the access these platforms have to your data closely. While leveraging their capabilities, ensure they do not compromise sensitive information.
Implement a Risk-Based Cybersecurity Approach
Even with the right cybersecurity policies in place, you cannot eliminate every risk. The best way to reduce your risk and avoid negligence is by taking a risk-based approach. Taking a risk-based approach to cybersecurity involves identifying potential threats, assessing their likelihood and impact, prioritizing them based on their severity, and developing strategies to mitigate these risks. Continuous monitoring and review ensure that the defenses remain effective and evolve with the threat landscape.
A risk-based approach to cybersecurity involves several key steps:
- Risk Identification: Document all potential threats and vulnerabilities. Use risk assessments, security audits, and historical data analysis to uncover risks.
- Risk Assessment: Assess the likelihood and impact of each risk. Consider the probability of threats exploiting vulnerabilities and the consequences of such events.
- Risk Prioritization: Assign risk levels to prioritize them based on their potential impact and importance to the organization.
- Risk Mitigation: Develop strategies to mitigate risks. This may include security measures like firewalls, encryption, and access controls, as well as employee training and incident response plans.
- Monitoring and Review: Continuously evaluate the effectiveness of your risk mitigation strategies. Stay updated with the evolving threat landscape to ensure your risk management remains relevant.
Security Risk Management software helps companies navigate the additional cybersecurity risks that come with remote work. By centralizing information in a unified repository, it provides businesses with crucial insights and prioritizes risks. This centralization is key to avoiding the pitfalls of negligence, as it ensures that all compliance information and IT security measures are consistently applied and monitored. The software’s ability to generate configurable reports and dashboards allows for real-time visibility into the organization’s security posture across siloes, enabling swift action on pressing risks and ensuring that nothing falls through the cracks. It acts as a safeguard against the costly consequences of negligence by keeping companies informed, compliant, and secure.
By embracing these strategies and tools, organizations can fortify their defenses against the ever-evolving threats of the digital age. The key to navigating the cybersecurity minefield is not just in the strength of the defenses but in the intelligence of the approach.