Role Authorization Software
Role authorization refers to the process of granting employees access to your organization’s programs, data and other privileged information. This is a critical step within the employee life cycle, so the responsibilities associated with this process are often appointed to the HR department.
However, there are so many moving parts involved in role authorization that it’s necessary to enlist the help of IT, Compliance, Finance, Operations, and many other departments. LogicManager offers a comprehensive Role Authorization solution that offers everything you need to facilitate cross-departmental communication, gain efficiencies, maintain compliance and create an enjoyable employee experience.
This application can be achieved through:
LogicManager’s Role Authorization Solution
Here’s what you can expect with LogicManager’s Role Authorization solution:
- Using LogicManager’s incident forms, manage both the initial authorization request, the follow-up, and conclusion of the process all in one place. Customize the questions on these incident forms, or leverage out-of-the-box fields that help you gather information that best suits your needs.
- Migrate existing forms and functionalities you rely on directly into the LogicManager application so that you don’t lose important information.
- Using our Role Automation Workflow, automate the role authorization request to ensure utmost efficiency when responding to requests. This workflow, along with many others, can be customized to automatically send tasks to stakeholders and expedite the process.
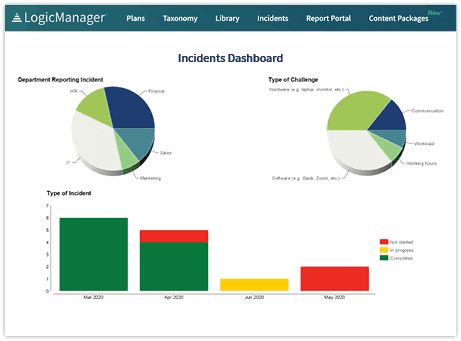
- Leverage a number of custom incident reports to track trends in your authorization requests. This also will allow you to pull records in the event you need to evaluate your request history. Commonly used reporting tools for role authorization include our Narrative Report and Chart-Based Analysis.
Build a Role Authorization Process with LogicManager
Maintain a centralized repository
With LogicManager, you can manage your role authorization process through a centralized repository of all requests that have been submitted. Having this holistic view also helps ensure that appropriate due diligence is being performed on all of these requests.
Automate your processes
Instead of requiring users to manually alert each other when a new request has been submitted or reviewed, LogicManager’s ERM platform automates this process. This ensures that all appropriate steps are being taken and allows you to track completion of those steps directly within the tool.
Ensure compliance
Your organization may be subject to role authorization regulations that require evidence that only necessary users have access to sensitive information. Having a formalized process in place for role authorization ensures that you can track when you are conducting those reviews and what the outcomes are.
What are the Risks of an Insufficient Role Authorization Process?
When users have inappropriate access to areas of your organization, it can lead to significant data and security risks – especially when there is sensitive information involved. A security incident such as a data breach can lead to financial losses for your customers and your business, and can cause you to fall out of regulatory compliance. This can lead to reputational damage and sanctions that may be irreparable in the long run.
Considering the employee life cycle, there comes a time for employee offboarding. Without a formalized process in place for auditing and removing access to sensitive information, there will be far more manual tasks to complete when it comes time to removing authorized users. This leads to an unnecessary amount of time being allocated to administrative tasks when your team could be focusing on achieving more strategic objectives.
Request a DemoLearn How LogicManager’s Role Authorization Tools Can Transform Your HR Risk Management Program
Speak with one of our risk specialists today and discover how you can empower your organization to uphold their reputation, anticipate what’s ahead, and improve business performance through strong governance.