When Banking Risk Workflows Don’t Match Reality
Last Updated: May 13, 2026
by Christian Parker
This is a perspective from Christian Parker, Senior Onboarding & Enablement Specialist at LogicManager. We’re sharing it because strong risk programs are not built through configuration alone. They are built when workflows reflect how risk work actually moves across teams, approvals, evidence, and ownership. In banking, especially, a process may look complete on paper, but if the sequence is unclear or the right people are not accountable at the right time, issues become harder to govern, explain, and scale. This is the kind of work we help customers think through at LogicManager: connecting process, ownership, and accountability so risk management becomes part of how work gets done, not just how work gets documented.
One thing I’ve noticed working closely with customers during onboarding and enablement is that risk programs rarely struggle because teams do not care about oversight. Most teams absolutely do.
The challenge is usually something else: the process documented in the system does not always match how work happens day-to-day.
In banking, that gap matters quickly.
Banks do not have the luxury of treating fraud, cybersecurity, operational risk, and compliance as separate conversations. A suspicious wire transfer is not just a fraud event. It may reveal a control weakness, expose a digital payments vulnerability, trigger customer impact, raise audit questions, or create regulatory scrutiny.
When those situations happen, speed matters, but so does discipline.
That is why, during onboarding, the most important conversations are often not just about configuration. They are about whether the system reflects how the customer’s risk work really moves.
The Disconnect We See Most Often
A lot of the banking teams I work with already have defined workflows.On paper, the process often looks straightforward:
- Alert intake
- Investigation and escalation
- Control adjustment
- Validation and closure
But underneath those steps, there is usually much more happening.
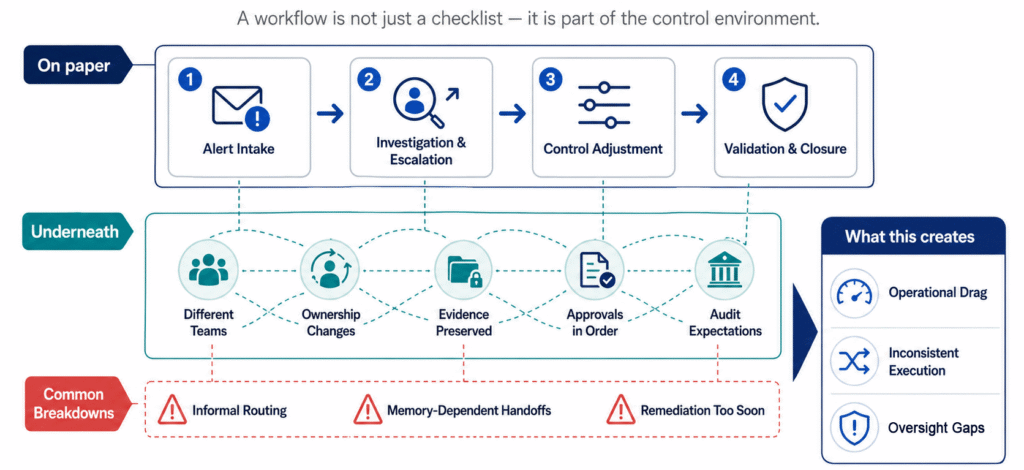
Different teams are involved. Ownership changes. Evidence needs to be preserved. Approvals need to happen in the right order. Audit expectations need to be met. That is where things can start to break down.
- Sometimes work gets routed informally.
- Sometimes ownership depends on someone remembering what comes next.
- Sometimes remediation happens before the investigation is fully understood.
None of those issues sound dramatic on their own.
But over time, they create operational drag, inconsistent execution, and oversight gaps that become difficult to explain to leadership, auditors, or regulators.
That is why I often tell customers that the workflow is not just a checklist. It is part of the control environment.
Why Sequencing Matters More Than Teams Expect
One thing that comes up often during onboarding is process sequencing.
For example, in a fraud or cybersecurity workflow, a digital payments alert should not move directly from “open” to “closed” just because someone completed a form.
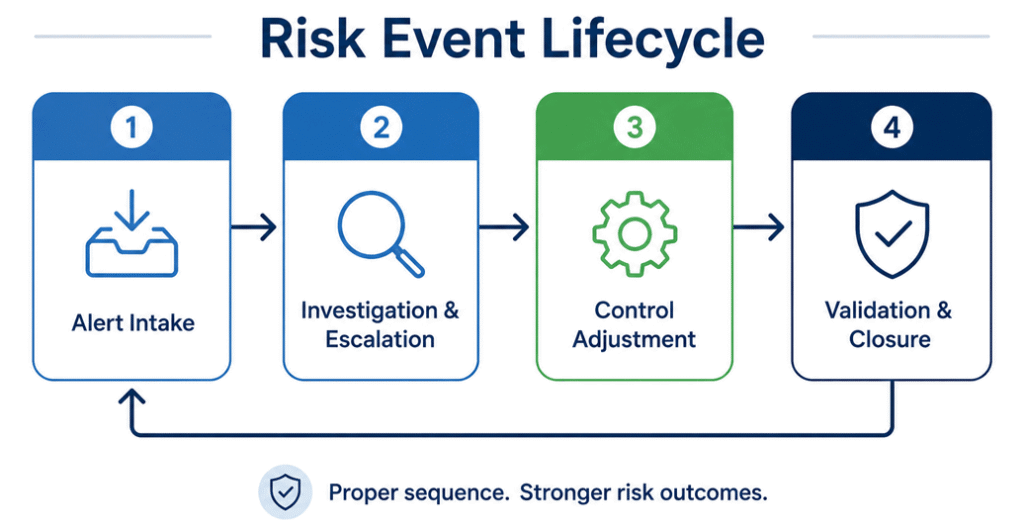
There is usually a lifecycle behind that event:
Alert Intake
A fraud-monitoring tool, SIEM, or other detection source creates the exception. An analyst reviews the event details, impacted channel, customer segment, amount, and control context before routing it.
Investigation and Escalation
A fraud or cyber analyst determines whether the issue is isolated or systemic and whether escalation or remediation is required.
Control Adjustment
A control owner updates thresholds, authentication requirements, alerting logic, or related procedures.
Validation and Closure
An independent reviewer confirms the control adjustment worked as intended and did not create unintended operational or customer impact. That sequencing matters.
A bank should not validate a control before remediation is completed. And the same person should not investigate the issue, adjust the control, and approve the outcome.
When the process sequence reflects how risk work happens, the system becomes much easier for teams to follow, explain, and govern.
Why Taxonomy Structure Ends Up Being More Important Than Expected
Another thing I’ve learned through onboarding customers is that taxonomy design is not just about organizing information. It becomes the foundation for how work is routed, governed, and understood.
For example, many banking teams structure workflows around processes like:
Banking Operations
→ Digital Payments
→ Security Monitoring
→ Alert Intake
→ Investigation and Escalation
→ Control Adjustment
→ Validation and Closure
When that hierarchy reflects the real operating model, teams spend less time working around the system and more time using it.
This is why enhancements like taxonomy sequencing and integrated reference fields matter. They help teams configure the platform around the way work is governed, not just the way information is categorized.
And honestly, that is where I see a lot of onboarding success happen. Not when teams simply configure workflows. But when they step back and ask:
“Does this structure reflect how our organization operates?”
The Bigger Shift: From Documentation to Operational Discipline
One thing I appreciate about working with banking organizations is that the strongest teams do not think about ERM as documentation. They think about it as an operational discipline. The goal is not just to log incidents. It is to create:
- clearer ownership
- repeatable processes
- stronger evidence
- better visibility for leadership
- and more defensible oversight practices
That is also why segregation of duties comes up so often in these conversations. The person investigating an issue should not also validate the outcome.
- The process should guide ownership.
- Not personal memory.
- Not informal handoffs.
- Not whoever happens to be available.
When the workflow aligns to the organization’s oversight model, risk management becomes much easier to sustain consistently.
What This Means for Banking Teams
The banking organizations that seem to mature the fastest are usually not the ones adding the most complexity. They are the ones creating more alignment between:
- process
- ownership
- evidence
- and operational reality
Because risk does not usually break down inside a single function. It breaks down between them. That is why the most effective risk programs are not just technically configured. They are operationally aligned.
From an onboarding and enablement perspective, that is the goal: help customers build the right alignment early, so their ERM program is easier to govern, easier to trust, and easier to scale.
